In this article we will cover how Threat Modeling improves Pentesting. It is the fourth article in a series about Threat Modeling.
Read previous articles here:
Intro to Threat Modeling part 4
How Threat Modeling improves Pentesting
In our previous article, we discussed the differences between Threat Modeling and penetration testing when it comes to timing, objectives and outcome. In short, they are two different animals. But we also said that there is a place for both techniques. They are both valuable tools in your security toolbox.
Even more, creating a Threat Model before performing a penetration test, will greatly improve the quality of your test.
Let’s get into why that is.
We know of three ways in which Threat Modeling improves your penetration tests: by improving reconnaissance, by providing scoping and by introducing business risk.
Threat Modeling as a reconnaissance phase
Threat Modeling is a great way of analyzing an IT system (or application) from the top down. It allows you to first see the bigger picture, the interdependencies of the system, before diving deeper into the areas where you want more details.
When you’ve done this exploration, the layout of the system is made very clear, and so is the attack surface.
This knowledge of the attack surface helps to prioritize time spent on different tests to be done. Pentesting time is limited (for most of us) and expensive: better to spend it where it matters!
Define your test scope by Threat Modeling
The Threat Model will not only give you a global overview of the system as a whole. It will also describe the ‘Trust Boundaries’. These are inflexion points where a security step-up or -down occurs. This implies that the Threat Model helps you to figure out what areas of the application are best to focus on when Pentesting.
The Threat Model provides an easy map to pinpoint where a test should be performed, what the scope should be.
This works in any testing scenario: white, grey or black box. In white or grey box tests, the scope is very clear and the data flow diagram (DFD) created during Threat Modeling can be part of the test input. In a black box scenario, the person giving the assignment can be very clear about the system areas that need to be tested without providing the overall DFD.
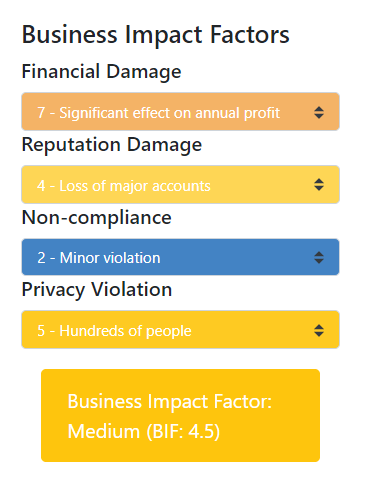
Example of OWASP business risk calculation
Using realistic risk ratings in your test
A Threat Model works with scenarios of security events – with a strong focus on ‘worst case’ scenarios. In the Threat Modeling practice, these scenarios are talked about in technical but also in business terms. This means the business impact of a security event is evaluated.
If a penetration test confirms a vulnerability, you can use these scenarios to provide a proper risk rating to the vulnerability. You defined the business risk during the Threat Modeling process. Use them in your test reporting!
Your penetration testing report becomes instantly more readable and usable by management, since the technical risk rating ( eg. OWASP or CVSS) are expanded to reflect the business risk, based on the impact of the potential breach! You finally get to use those business impact calculators in the OWASP risk calculator!
Our next article is, you guessed it: ‘How Pentesting improves Threat Modeling’.
Here you can find all our content about Threat Modeling.
Dive into our Threat Modeling Insider Newsletter archive and subscribe to become a Threat Modeling PRO!