Shostack, A. (2024). Keynote address. OWASP Global AppSec Conference.
Shostack, A. (2014). Threat Modeling: Designing for Security. Wiley.
Tversky, A. & Kahneman, D. (1973). Availability: A heuristic for judging frequency and probability.
Cognitive Psychology, 5(2), 207–232.
Slovic, P., Finucane, M., Peters, E. & MacGregor, D.G. (2004). Risk as analysis and risk as feelings. Risk
Analysis, 24(2), 311–322.
Sunstein, C.R. (2002). Risk and Reason: Safety, Law, and the Environment. Cambridge University Press.
Goodhart, C. (1975). Problems of monetary management: The U.K. experience. Papers in Monetary Economics,
Reserve Bank of Australia.
Campbell, D.T. (1979). Asshole for the social scientist. American Behavioral Scientist, 23(3), 85–95.
Centola, D., Becker, J., Brackbill, D. & Baronchelli, A. (2018). Experimental evidence for tipping points in
social convention. Science, 360(6393), 1116–1119.
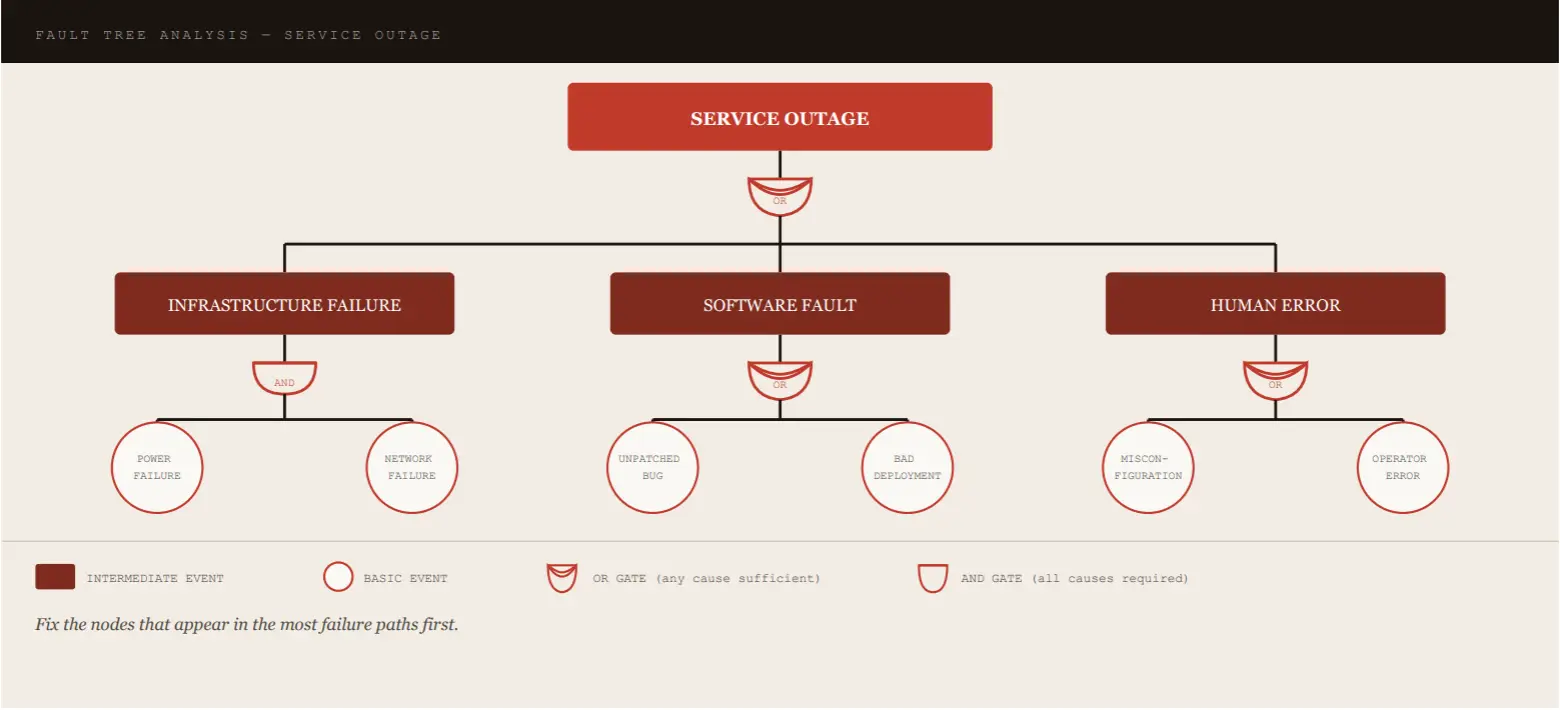
Schneier, B. (1999). Attack trees: Modeling security threats. Dr. Dobb’s Journal.
Schoenfield, B. (2015). Securing Systems: Applied Security Architecture and Threat Models. CRC Press.
Schoenfield, B. (2021). Secrets of a Cyber Security Architect. CRC Press.
Schoenfield, B. (2024). [Casino maths etc.]. LinkedIn posts and OWASP Slack conversations.
Young, R. (2024). [On scenario-based security decision making]. LinkedIn post.
Lantzy, S. (2024). [On killing the risk matrix]. LinkedIn post.
Marx, K. (1843). Letter to Arnold Ruge. Deutsch-Französische Jahrbücher.
NCSC (2025). Annual Review 2025. National Cyber Security Centre, UK.
OWASP Threat Model Library. https: /owasp.org/www-project-threat-model-library/