Written by Laurent Dupont
Welcome
Hi there.
Welcome to the June edition of Threat Modeling Insider in 2022!
This edition contains various fields in which Threat Modeling can play a significant role: MDR, AI/ML, Automation, Pentesting and User Stories. Exciting!
Our complete TMI Line-up:
- “We need an army of threat modelers”, interview with a specialist in security regulations for medical devices, Seth Carmody
- Curated content: Plot4ai. How to threat model AI and ML?
- Curated content: Machine-assisted threat modeling. How to speed up and improve threat modeling?
- Toreon Blog Post: Can Threat Modeling improve pen testing?
- Toreon Tip: When does a user story warrant a threat model update?
“We need an army of threat modelers”
Interview with a specialist in security regulations for medical devices, Seth Carmody
Threat modeling is gradually finding its way in the R&D processes of medical devices, with the FDA being one of the main driving forces. We had a conversation with Seth Carmody, Vice President of Regulatory Strategy at MedCrypt and former Cybersecurity Program Manager, Medical Devices at FDA.
Drawing on his ten years of medical device experience, Seth provides strategic direction for cybersecurity products and services for the regulated medical device market. At FDA (U.S. Food and Drug Administration) he spent 8 years architecting technology policy and laws that impact software-enabled medical devices, such as the FDA’s medical device cybersecurity policies.
Can you describe your background and how you got into medical device cybersecurity?
“I studied organic chemistry in graduate school, which prepared me well for an opportunity at FDA to work in diabetes devices. Part of my role at FDA was to review software for these medical devices.
In 2013, a security researcher submitted their research to us; this research included hundreds of devices. In that time the Center for devices, had no mechanisms, policies, let alone expertise to deal with this information. The group charged with the task of dealing with all the research information came to me and said, ‘Hey Seth, you like software, don’t you?’, and handed me the files. That launched me into an incident response role which evolved to include technology policy so that we could get ahead of post-market issues. It’s through these roles that I picked up a lot of knowledge about cybersecurity for medical devices.”
What is your experience with threat modeling?
“As a practitioner, very little. However, the advantage of not being a specialist is that you are able to see the big picture about how threat modeling fits within the existing medical device regulation. I remember the conversations with experts in 2014 about how threat modeling was going to be important. If you look to the FDA postmarket guidance that was finalized in 2016, you will find in the appendix a section on threat modeling. At the time my conception of where it would fit in the world was not really solidified.
In the 2018 draft premarket guidance and the re-release of that draft in 2022, you see that threat modeling is taking on an increasingly important role, as the driving force for everything else regarding medical device security. That has been my evolution as a policy writer. You feel something is important, but you do not know where it exactly fits and how important it will be, but gradually you learn by observation and from other experts where it fits. Threat modeling has really become the security risk assessment staple.”
What is the relation between threat modeling and other security activities as part of the FDA guidance?
“If you are a professional in IT security, you have a world that is very mature. In the medical device space, we are really in a transition period. Medical devices have always been built without security in mind. That is not because of some miss on the part of the medical device manufacturers, they just focused on delivering the best medical features. That was their core business. Now we are in a transition period where security features should be considered in the early stages of the R&D processes. You see that threat modeling is a centerpiece within that transition period and it drives decisions about the security controls that should be implemented.
Medical devices typically do not come with standard security controls. Threat modeling helps to define and crystalize the security controls needed to assure medical device cybersecurity.
Another important pillar is making clear what the value of threat modeling is for the business. It is the main struggle that security specialists are dealing with. Some medical device manufacturers ask themselves why they should take the effort and how it will benefit the business. We must make it clear that, although it might be an extra cost in the development stage, it will pay off later on, in terms of reputational savings and forced redesigns in the future.”
What is your prediction for the final version of the FDA Guidance on Cybersecurity in Medical Devices and when will it become “active”?
“The draft was finalized in 2022 and the commenting period ends in the beginning of July. It will take a month or two for the internal team at FDA to process all the comments and alter the document where needed. It will go through different layers of review before it is passed to the official guidance clearance process. That will be sometime around the fourth quarter of this year.
The final approval process takes up another nine months. So, we are looking at Q3 of 2023.
However, some things can influence the timeframe.
During covid the health care sector was mainly focused on fighting the pandemic, leaving fewer resources in commenting, editing and approving guidance documents. So, things like that delay the whole process dramatically.There are also other factors that can compress the approval period. If the U.S. President or the US FDA Commissioner, Robert Califf, state that the policy is important to get out, it can move a lot faster. If the Commissioner expedites the clearance process, we could see it finalized in October 2022, if not I would say Q1 of 2023.
You are a contributor and bootcamp facilitator of the MDIC – Playbook for Threat Modeling Medical Devices. What is your take-away from this?
“The playbook was co-built by lots of industry experts, but primarily facilitated by the MDIC (Medical Device Innovation Consortium), MITRE, and FDA. MDIC is a consortium that is funded by the industry, working on industry-wide problems. For me it was obvious that threat modeling is one of those industry-wide problems that needs an industry-level effort.
We launched a project with different stakeholders and manufacturers with the aim to make a playbook, with examples, that help people through the threat modeling process.
The takeaway from it is twofold.
To be successful in this industry, we need an army of threat modelers. We need specialized people that really get threat modeling and are in that security minded space. And we also need a thin layer of threat modeling for everybody, maybe even you. If you stimulate everybody to start thinking in a threat modeling way, it will raise the bar and the level of security for medical devices and medical technology. If a regulatory affairs person receives threat modeling training, and they see the engineers come up with some piece of documentation with respect to cybersecurity or threat modeling, they will understand the value of this. It builds a security minded foundation for everyone.
The MDIC Playbook is a good start in terms of rallying different stakeholders around the issue of threat modeling and working through some of the issues. The goal is to raise the bar a little bit and try to pass through the built-up knowledge to the rest of the industry.”
What is your recommendation for any medical device manufacturer who considers a pre-market submission?
“There are a few factors that contribute to what I would call the uncertainty for anyone who is looking to submit.
First, the 2022 guidance is in draft and not for implementation. So technically, the only guidance that is valid for implementation is the 2014 version, which is solid, but insufficient. The catastrophic impact of cybersecurity issues which we have seen recently – think WannaCry – tells us that we cannot wait to start implementing threat modeling.
Basically, when you submit as a manufacturer before the official release of the new guidance, you may get a reviewer that says “show me your threat model” or you may get a reviewer that does not.
I would recommend medical device manufacturers to always do a pre-submission. It’s a cost-free submission to the FDA to ask any question you want. You can send in your threat model, ask questions, and get feedback. Or just ask them what they expect in terms of threat modeling. That way you get information before you submit.
If you submit and the FDA tells you they need a threat model, you will have to dive in. Luckily, that does not have to be complicated. With the right focus and the right people, you will arrive at something that will hit all the major risks and cover them in a reasonably short time. It is a continuous process, but you can start pretty easily, and you will get something that will be submittable to the FDA.”
How can we make threat modeling more effective for a medical device development team?
“As said before: we need more threat modelers, so a training that is focused on the medical device space would benefit the industry greatly. And for that, we can draw on training that is already built.
Secondly, the value of threat modeling should be articulated. We have to come to a point where medical device developers automatically say: ‘We need security controls here, here, and here. How do we do it? What will it cost? How much time will it take to implement?’ These are all important questions for the business that are trying to meet market demands.”
Guest article by Seth Carmody
Book your seat in our Threat Modeling Medical Devices Course!
Toreon’s Data Protection Institute (DPI) and MedCrypt have partnered to create the most comprehensive threat modeling training specifically for Medical Device Manufactureres (MDMs).
Learn how you can leverage your threat model in multiple other aspects of your regulatory submission, allowing you to focus on addressing any issues rather than assembling a multitude of different documents.
Every medical device needs a threat modeler, but not every threat modeler needs to be a cybersecurity specialist. Through our training every participant will walk away with both knowledge about threat models, how to assemble a team and conduct a session as well as all of the materials to do that the very next day.
Curated threat modeling content
Plot4.ai
Do you have experience with LINDDUN GO, an approach for Privacy Threat Modeling? And/or are you working with AI/ML and are you interested in privacy by design and responsible AI? Then you will love Plot4.ai! Plot4ai is an adaption of LINDDUN, focused on artificial intelligence and machine learning. It has been created by Isabel Barbará and it contains 86 threats, divided over 8 categories.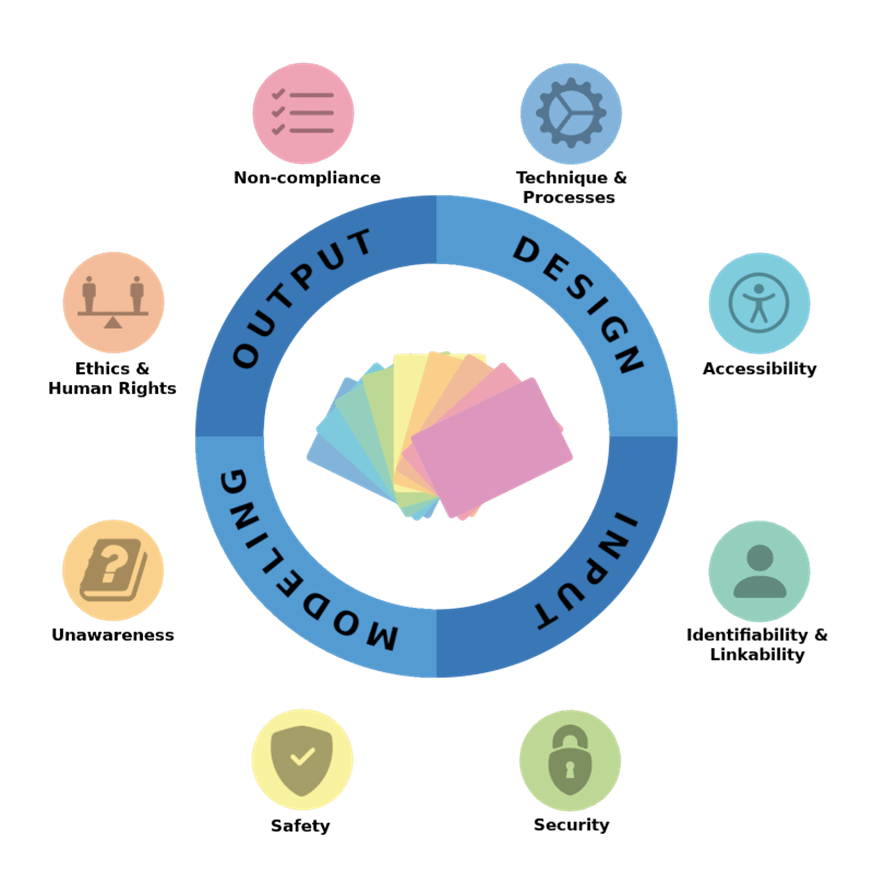
You can contribute by giving feedback on the content or sending input for new threats via GitHub. Furthermore, if there is enough interest, PLOT4ai will be taken to the next level, and it will be continued as a community driven project.
Machine Assisted Threat Modeling
As fans of the Application Security Podcast show, we can only but recommend the latest episode on Threat Modeling. In this episode hosts Chris Romeo and Robert Hurlbut talk with Kristen Tan and Vaibhav Garg. They wrote a paper called “An Analysis of Open-source Automated Threat Modeling Tools and Their Extensibility from Security into Privacy”. In the paper and during the show they explain their quest on ways to threat model not only faster (automated) but also better.
You can find the show on your favorite podcast platform.
Toreon blog post: How Threat Modeling improves Pentesting
In our previous article, we discussed the differences between Threat Modeling and penetration testing when it comes to timing, objectives and outcome. In short, they are two different animals. But we also said that there is a place for both techniques. They are both valuable tools in your security toolbox. Even more, creating a Threat Model before performing a penetration test, will greatly improve the quality of your test. Read all about it here.
This is the fourth post in our series about Threat Modeling. The series is meant to provide basic information about the practice of Threat Modeling, why we love it and how it can make your organization more secure.
Toreon tip: User stories and Threat Modeling
When does a user story warrant a threat model update?
Let’s assume there is an agile development team (SCRUM) that already has an up-to-date threat model. What will typically happen?
- The user stories for the next sprint will be evaluated in the refinement meeting and planned in the sprint planning meeting.
- During the refinement meeting a risk analysis is made. If the analysis shows that there is a new risk or if an existing risk needs to be updated, then the threat model will most probably be updated as well.
- During the sprint planning the risk analysis is used to ensure the required security effort is also incorporated in the planning.
However, this process does not yet show how and/or when a user story will vindicate an actual update of the threat model. This is a little bit more difficult to capture in hard rules. But here are our guidelines.
So, update your threat model when in the user story:
- The functionality is new.
- The business logic changes.
- A security control or dependency (e.g., authentication or authorization) changes.
Lastly, when the functionality is just extended an update is possible, but often not required.
We aim to make this a community-driven newsletter and welcome your input or feedback. If you have content or pointers for the next edition, please share them with us.
Kind regards,
Sebastien Deleersnyder
CTO, Toreon
Book a seat in our upcoming trainings
- Advanced Whiteboard Hacking – aka Hands-on Threat Modeling (Black Hat USA, Las Vegas) (2-day trainings starting on 6 or 8 August)
- Threat Modeling Medical Devices training (online through DPI) (next cohort start on 19 August)
- Threat Modeling Practitioner training (online through DPI) (next cohort start on 12 September)
- Advanced Whiteboard Hacking – aka Hands-on Threat Modeling (BruCON, Belgium) (27-28 September)
We also organize in-company training for groups as of 10 participants.